Bad USB Payload Lab
A hardware-focused project for building and testing keystroke injection payloads that simulate real endpoint compromise scenarios, operator tradecraft, and user-assisted execution paths.
Project Details / Background
This project was built to study how physical access and trusted-device assumptions can be abused during short, high-impact engagements. The focus was not just on payload execution, but on understanding how endpoint controls, user privilege levels, and execution timing affect real-world success rates.
Using a Bad USB platform, I developed and tested payload chains that simulate operator actions such as scripted command execution, staged downloads, credential collection attempts, and rapid host configuration changes. The main objective was to observe what works reliably, what fails under defender controls, and what indicators are created on the endpoint.
What I Built / Tested
The lab focused on keystroke injection workflows, payload reliability, execution delay tuning, and environmental checks before running sensitive actions. This made the project useful for understanding how physical attack vectors interact with user sessions, application focus, language settings, USB trust, and local security tooling.
I used it to explore how different payload styles behave across Windows systems, including command shell launches, PowerShell-based execution, staged operator actions, and automation designed to minimize visible user disruption. Testing emphasized both exploitation logic and defensive visibility.
Security Value / Takeaways
This project demonstrates practical understanding of physical attack vectors, endpoint assumptions, and the gap between payload theory and real execution reliability. It also reinforces the importance of device control policies, user awareness, application whitelisting, and endpoint monitoring against rapid scripted actions.
From a defender perspective, the project helped highlight which host events and user behaviors should be watched more closely when investigating suspicious USB activity or short-lived operator actions on a workstation.
Gallery / Notes
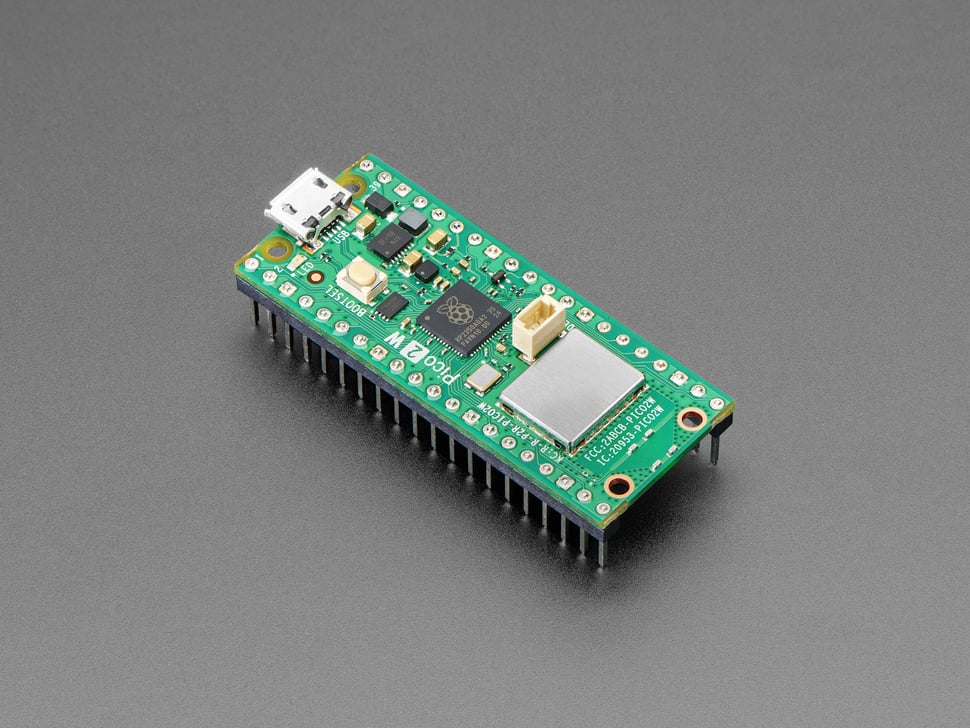
 Bad USB hardware used to test rapid payload execution and operator timing.
Bad USB hardware used to test rapid payload execution and operator timing.
 Payload development emphasized reliability, staged execution, and environmental awareness before sensitive actions.
Payload development emphasized reliability, staged execution, and environmental awareness before sensitive actions.
 Used to study how physical access can translate into endpoint compromise attempts under real workstation conditions.
Used to study how physical access can translate into endpoint compromise attempts under real workstation conditions.